Since 2017 and as a result of the Bangladesh Bank cyber heist, SWIFT established a Customer Security Programme which describes a set of mandatory and advisory security controls for participants. All customers need to re-attest and confirm full compliance with the mandatory security controls. As stated by SWIFT’s CEO in May 2016:
The Bangladesh Bank hack was a watershed event for the banking industry. There will be a before and an after Bangladesh. The Bangladesh fraud is not an isolated incident … this is a big deal. And it gets to the heart of banking".
SWIFT’s CSP security controls can significantly reduce the risks of being breached. Moreover, as proofs of compliance can be requested by counterparties, it is also about reputation and business. In other words, the challenge is to stay secure and trusted within the SWIFT network. From our point of view, the CSP is often misunderstood: it shouldn’t be considered as a “simple” compliance checklist. The key point of the compliance process is to consider the risk drivers (the “spirit” of the CSP) in order to assess an implemented architecture and define new security controls if needed. Keeping the right balance between business needs, usages and security (not limited to SWIFT CSP requirements) the framework is a real chance to strengthen a cyber security posture and thus prevent malevolent attacks.
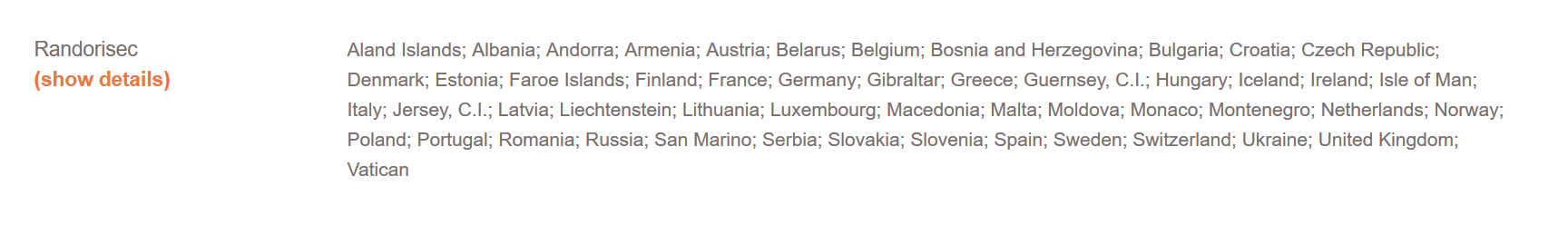
Since the beginning of this process RandoriSec offers services specifically dedicated to provide assistance to meet the SWIFT CSP goals and requirements but we’ve recently decided to go one step further by dedicating a team to this purpose and being listed as a cyber security service provider in SWIFT CSSP directory*, providing services over the Europe area.
If you want to discuss any CSP related topics, feel free to contact us!
*SWIFT does not certify, warrant, endorse or recommend any service provider listed in its directory and SWIFT customers are not required to use providers listed in the directory.