Guillaume Lopes
Training
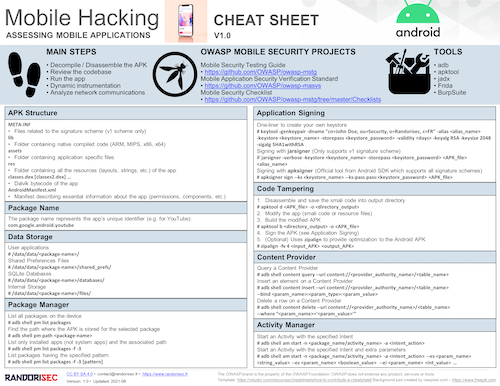
Training During the DeepSec event, we gave our Mobile Hacking training (this training was also provided at Hack In Paris).
This training presented the toolset needed when assessing mobile applications (such as adb, Apktool, Jadx, Androguard, Cycript, Frida, Needle and MobSF) and, also, the techniques to help you to work faster and in a more efficient way in the mobile ecosystem. This 2-days training focused on Android and iOS applications. The main topics of the training were: