We are pleased to announce that we are going to give a new session of our Mobile Hacking training in an online form!.
Save the date June 21, 22 and 23 2021.
Here is the pitch of the training:
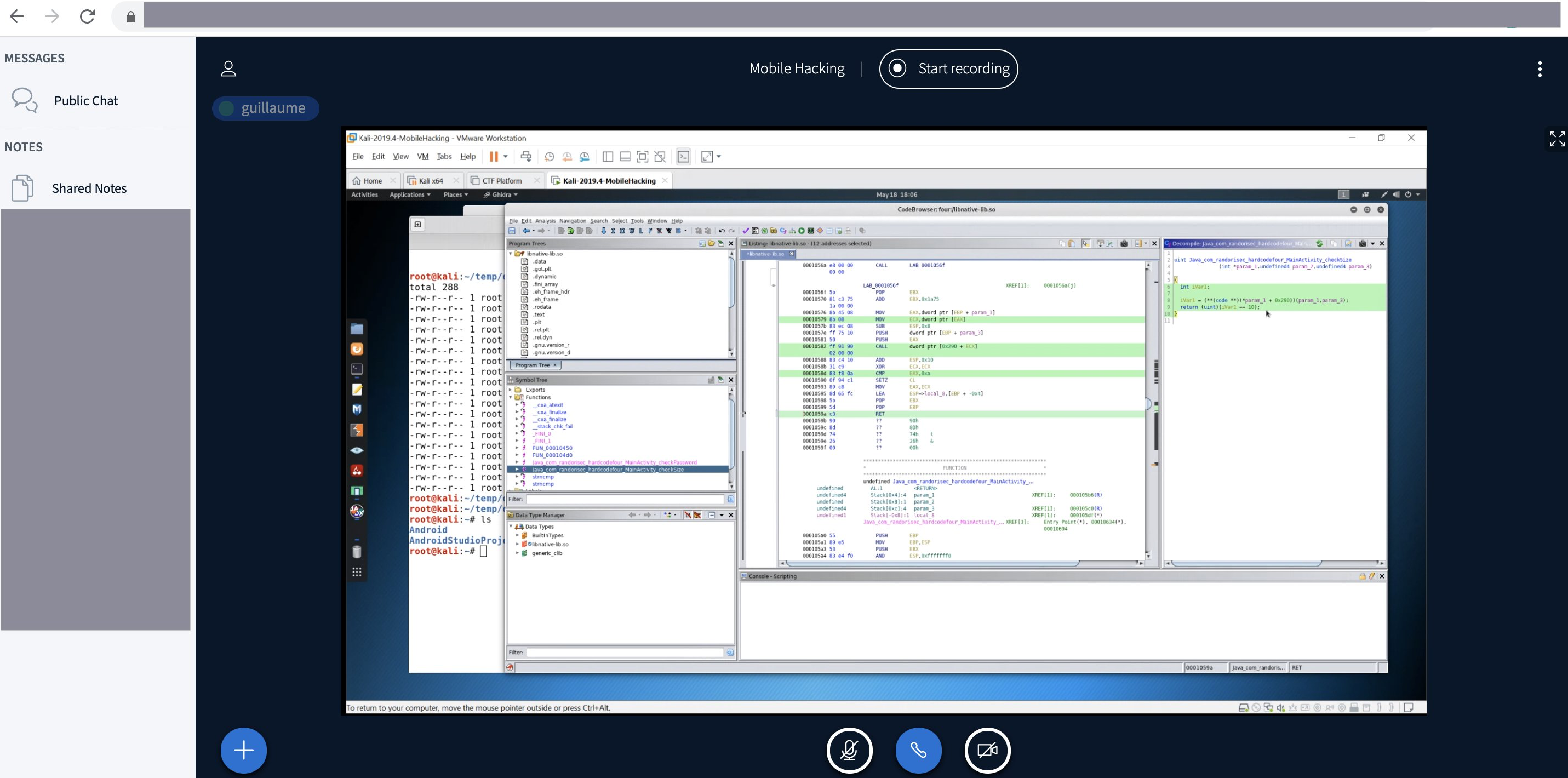
Guillaume Lopes and Davy Douhine, senior pentesters, will share many techniques, tips and tricks to deliver to pentesters, bug bounty researchers, app makers or just curious a 100% hands-on 3 days mobile training. Goal is to introduce tools (Adb, Apktool, Jadx, Ghidra, Objection, Cycript, Frida, Hopper, etc.) and techniques to help you to work faster and in a more efficient way in the mobile (Android and iOS) ecosystem. This is the exact training that you would have liked to have before wasting your precious time trying and failing while trying to assess the security of mobile applications.
Our online training is not based on recorded videos but on live sessions with the trainers.
Of course, attendees will have access to the slides and the labs to train on their own but they’ll also have interactive session with the trainers to do the labs together and ask questions. Also a one to one session with each attendee will be planned to debug problems and study specific subjects.
A Virtual Machine will be provided to the attendees with the pre-installed tools to cover most of the labs. In addition, a Corellium access (iOS virtualisation) will be provided. A big thank you to Corellium for making this possible.
Contact us if you’re interested: sales@randorisec.fr
Who Should Attend
Anyone who want to learn how to assess mobile applications with some prior knowledge on web security:
- Intermediate to experienced Pentesters
- Bug Hunters
- Security Researchers/Experts/Managers/Architects
- Mobile Developers
Prerequisite Knowledge
Network and linux basics
Key Learning Objectives
- Introduce the OWASP MSTG (Mobile Security Testing Guide) and the MASVS (Mobile Application Security Verification Standard)
- Learn Android and iOS security basics
- Know how to build an Android and iOS pentest toolset
- Learn how to review the codebase of a mobile application (aka static analysis)
- Run the mobile application on a rooted device (to check data security issues)
- Inspect the app via instrumentation and manipulate the runtime (aka runtime analysis)
- Man in The Middle all the network communications (aka inspect the traffic)
Hardware / Software Requirements
A laptop with:
- 8GB of RAM at least, ideally 16GB
- 50Gb of free space (to install a VM based on Kali that we’ll provide)
- Administrative privileges on your laptop + a way to deactivate anti-virus, HIPS and firewall
- VMWare Player (ideally VMWare Workstation)
- A PDF reader
Agenda
You can download the full program.